Twistlock
This one is going to be a very quick one… So… First off, I’d like to start by saying that personally, I love twistlock, it’s such a powerful tool, honestly, I find it fascinating how powerful it is, as an application developer, I use it to scan the OS that the application will be running on in my teams AKS cluster & of course the dependencies that the application utilises.
As an example of just how powerful it is, initially it noticed ~210 vulnerabilities in one of our containerised applications, within 3 hours I was able to reduce that down to a mere 32. I mean some of these vulnerabilities included technologies that in our use case are somewhat irrelevant, but of course, working in a financial institution, the more security the better. I mean for me personally, it’s been an immense tool in teaching me more about levels related to our architecture that I wouldn’t normally think about. Such as ensuring that the OS layer is as secure & stable as possible, even if it’s updating or removing dependencies that we wouldn’t normally use; a prime example being python, my team currently focuses on Java & in our applications we have nothing to do with Python. However, to reduce the number of vulnerabilities with our images, why not simply update or remove such dependencies?
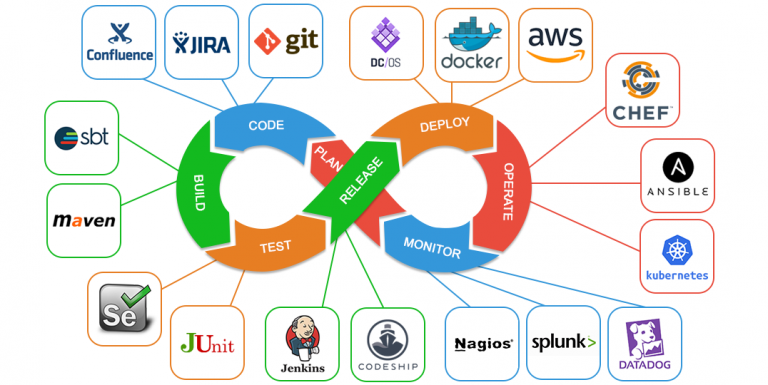
One feature that I love about Twistlock is that we’re able to integrate it into our build pipeline, so even without continuous monitoring of the Twistlock dashboard, if a high vulnerability is discovered, the build will fail, which also ensures that we’d never release/deploy insecure code into our cloud ecosystem. With Twistlock, it’s really teaching me to analyse everything possible, even things as detailed as the dependencies that our application servers use. It’s really forcing me to consider whether or not our application server even needs these dependencies, if so, could it be replaced with a newer version?
I’m still far from being a security specialist, very far from it, but it’s most certainly something that I think about more often. However, I have reached scenarios where I’m a little stuck, such as Twistlock finding known vulnerabilities where there’s no known fix, or where there’s something that’s so low level that changing it could cause for breaking changes, etc.